Polynomial-time exploit for ECC over rings using the Smart-Satoh-Araki p-adic attack.
Documenting the intersection of cybersecurity, advanced mathematics, and system internals.
Polynomial-time exploit for ECC over rings using the Smart-Satoh-Araki p-adic attack.

A research-based approach to breaking Elliptic Curve Cryptography defined over the ring $Z_p^3$ using the Smart-Satoh-Araki p-adic lifting attack.
An in-depth analysis of a SUID binary logic flaw where unsafe environment variable parsing enables arbitrary file read and full root compromise.
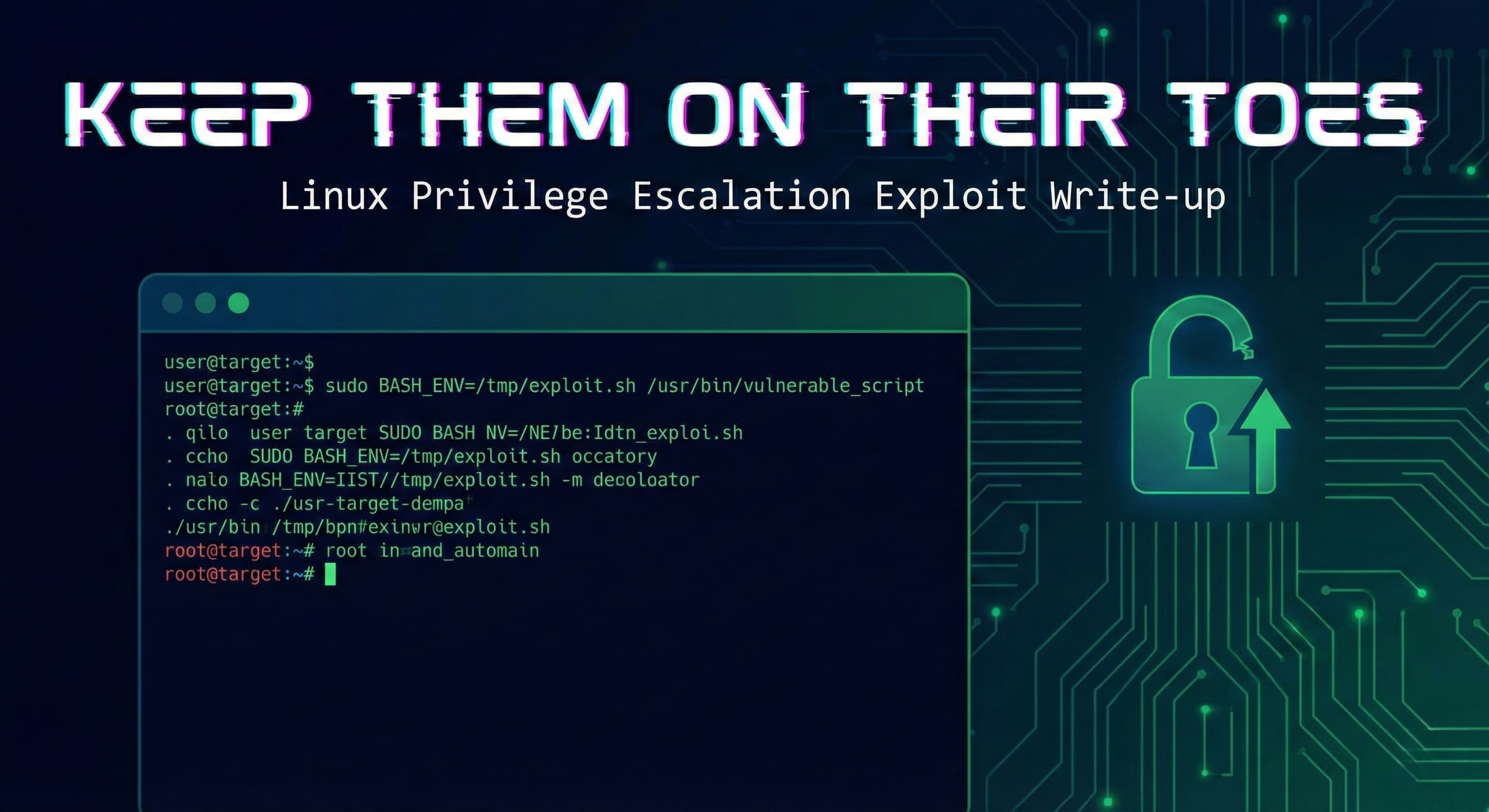
A detailed technical walkthrough of Linux privilege escalation via sudoers env_keep misconfiguration and BASH_ENV environment injection.

دليل عملي لهندسة الخصوصية، يشمل الخصوصية منذ التصميم، الامتثال القانوني، تقنيات تعزيز الخصوصية، والتطبيقات الواقعية.

A practical guide to Privacy Engineering, covering privacy-by-design, legal compliance, privacy-enhancing technologies, and real-world implementation.
دليل عمليات قياسي (SOP) لتطبيق مبدأ الدفاع في العمق (Defense in Depth). يغطي تأمين النواة، تفعيل SELinux، عزل الشبكة، واكتشاف الثبات (Persistence) للتهديدات.
A comprehensive, defense-in-depth SOP for hardening Fedora Linux workstations. Covers Kernel self-protection, SELinux enforcement, network isolation, and persistence hunting.