Featured
Technical Whitepaper: Anomalous ECC over Ring $Z_p^k$ via p-adic Lifting
Polynomial-time exploit for ECC over rings using the Smart-Satoh-Araki p-adic attack.
Deep dives into system exploitation and vulnerability assessments.
Polynomial-time exploit for ECC over rings using the Smart-Satoh-Araki p-adic attack.

A research-based approach to breaking Elliptic Curve Cryptography defined over the ring $Z_p^3$ using the Smart-Satoh-Araki p-adic lifting attack.
An in-depth analysis of a SUID binary logic flaw where unsafe environment variable parsing enables arbitrary file read and full root compromise.
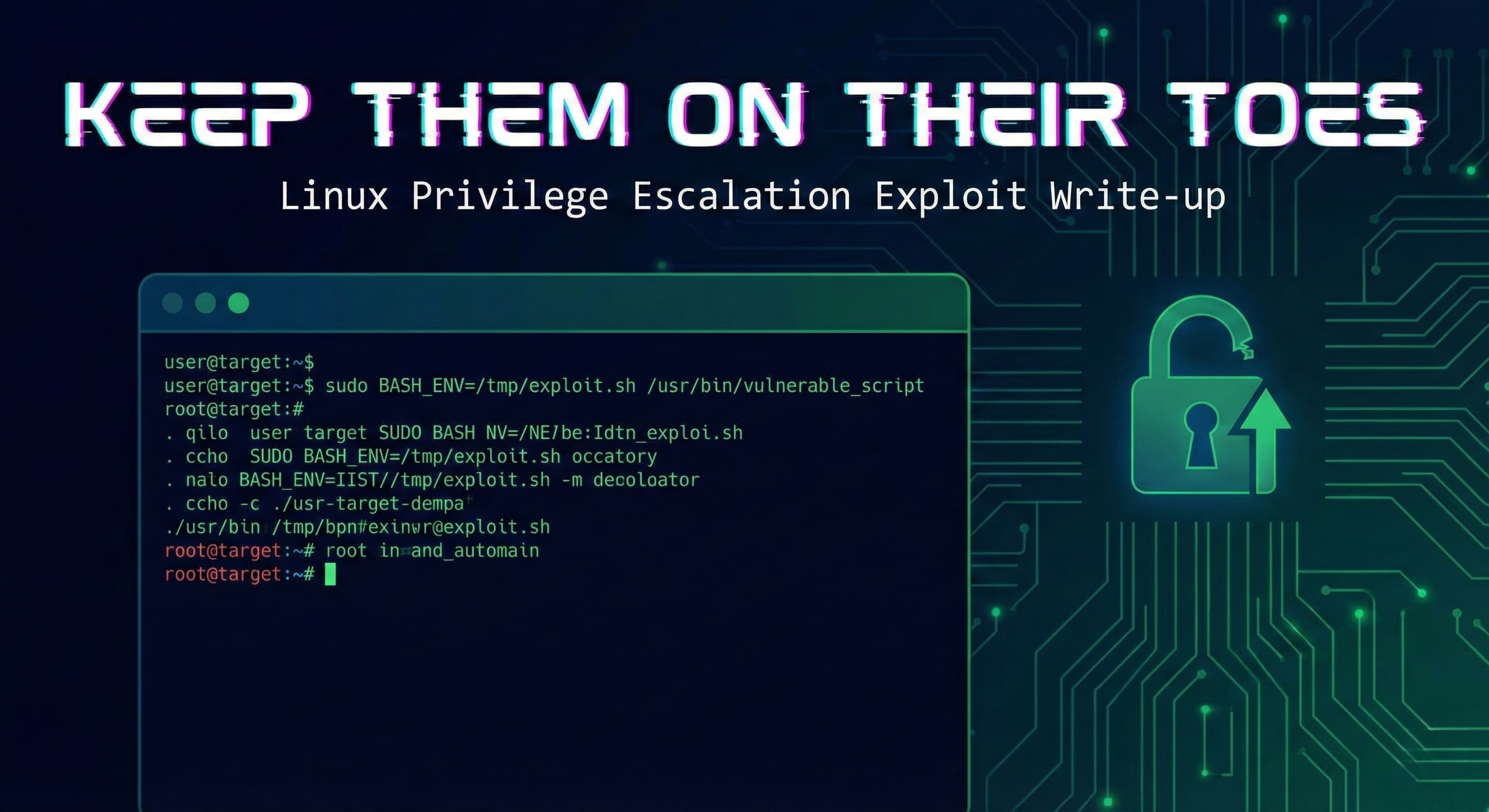
A detailed technical walkthrough of Linux privilege escalation via sudoers env_keep misconfiguration and BASH_ENV environment injection.